ISO 27001 Penetration Testing: Guide for Audit-Ready Security Testing
Last updated:18 March 2026
The question of how much technical testing is actually needed to pass an ISO 27001 audit is relevant for security leaders from different industries. The standard requires organizations to prove that their security controls work in practice, so ISO 27001 penetration testing is frequently discussed during implementation and audit preparation.
The pressure to demonstrate real security assurance is increasing. Gartner estimates that more than 60% of organizations will treat cybersecurity risk as a primary business risk by the end of 2026. In this environment, companies implementing ISO 27001 must show that their controls are tested, risks are validated, and vulnerabilities are addressed before attackers exploit them.
Our guide explains how penetration testing fits into an ISO 27001 Information Security Management System (ISMS). You will learn when testing is expected during certification, how to define the right scope, what testing methods provide useful evidence for auditors, and how to choose a qualified testing partner. The goal is simple: help organizations run security testing that supports both real protection and audit readiness.
Key takeaways
- ISO 27001 requires organizations to prove that security controls are effective and aligned with risk.
- Technical validation activities help demonstrate that protections work under realistic conditions.
- Auditors prefer penetration tests conducted according to established frameworks like OWASP or NIST SP 800-115.
- Testing should include all high-risk systems, such as public-facing web applications, cloud infrastructure, and internal networks.
- Properly scoped security testing strengthens both the ISMS and audit preparation.
- When choosing an ISO 27001 penetration testing company, it is important to ensure they have a proven track record of conducting successful penetration tests.
- Timing, scope, and methodology determine whether testing provides useful certification evidence.
- Well-planned penetration testing ISO 27001 activities help organizations validate controls, reduce risk, and support long-term security improvement.
What Is ISO 27001 Compliance, and Why Is It Important?
ISO 27001 is an international standard for managing information security. It provides a structured approach to protecting sensitive information through risk management, security controls, and continuous improvement.
ISO 27001 compliance means an organization follows the requirements of this standard and operates an information security management system (ISMS). This system helps identify potential threats, assess risks, and apply controls that protect important data and systems.
The framework focuses on three core principles of information security: confidentiality, integrity, and availability. In practice, organizations implement policies and technical safeguards that control access to data, secure systems, monitor risks, and respond to security incidents.
For many companies, the standard also serves as a signal of reliability. It shows customers, partners, and regulators that security processes are not random or reactive. Instead, they follow a structured and internationally recognized approach to protecting information.
Penetration testing of a cloud-native hospital management system before the annual ISO 27001 audit
What Is Penetration Testing in the Context of ISO 27001?
Penetration testing is a controlled security exercise that simulates real-world attacks on systems, applications, or infrastructure. Its main goal is to find weaknesses before an attacker does and understand how those weaknesses could affect the organization.
Within an ISO 27001 ISMS, penetration testing helps verify that security controls work as intended. Policies and procedures define how security should operate, but testing shows whether those protections actually hold up in practice.
This type of assessment supports the risk management process. When a penetration test identifies a vulnerability, the organization can evaluate the risk and decide how to address it. The result may include fixing the issue, improving a control, or adjusting the security strategy.
Penetration testing also provides evidence that technical safeguards are regularly reviewed and validated. This is important when demonstrating that security controls are not only documented but also actively maintained and tested.
The ISO 27001 penetration testing requirements are therefore often discussed in the context of assurance activities. The test itself does not grant certification. Instead, it serves as one way organizations evaluate the effectiveness of their security controls within the broader ISMS framework.
Is Penetration Testing Required for ISO 27001 Certification?
The short answer is: it depends. The standard does not prescribe a fixed list of technical tests. Instead, it expects organizations to demonstrate that their security controls work in practice. Evidence must align with the organization’s risks, systems, and scope of the Information Security Management System (ISMS).
This is why the answer to the question "Does ISO 27001 require penetration testing?" is not always the same for every organization. What matters is whether the chosen assurance methods can show that security controls are effective and appropriate for the identified risks.
ISO 27001 requirements vs annex A controls
ISO 27001 defines the structure and requirements for an ISMS. It focuses on governance, risk management, and continuous improvement. The standard itself does not mandate specific tools or technical activities.
Annex A provides a catalogue of security controls that organizations may adopt to address identified risks. These controls include areas such as vulnerability management, monitoring, and secure system development. The organization selects relevant controls and documents them in the Statement of Applicability (SoA), explaining which controls are implemented and why.
Risk-based justification and scope impact
ISO 27001 follows a risk-based approach. Each organization assesses threats to its systems and data, then decides which controls and verification methods are appropriate.
If systems process sensitive data, expose services to the internet, or support critical operations, stronger validation methods may be necessary. In such cases, technical assessments such as pentesting services may be chosen to verify that protections are working. In other environments, different assurance techniques may be considered sufficient.
When audits typically expect technical testing evidence
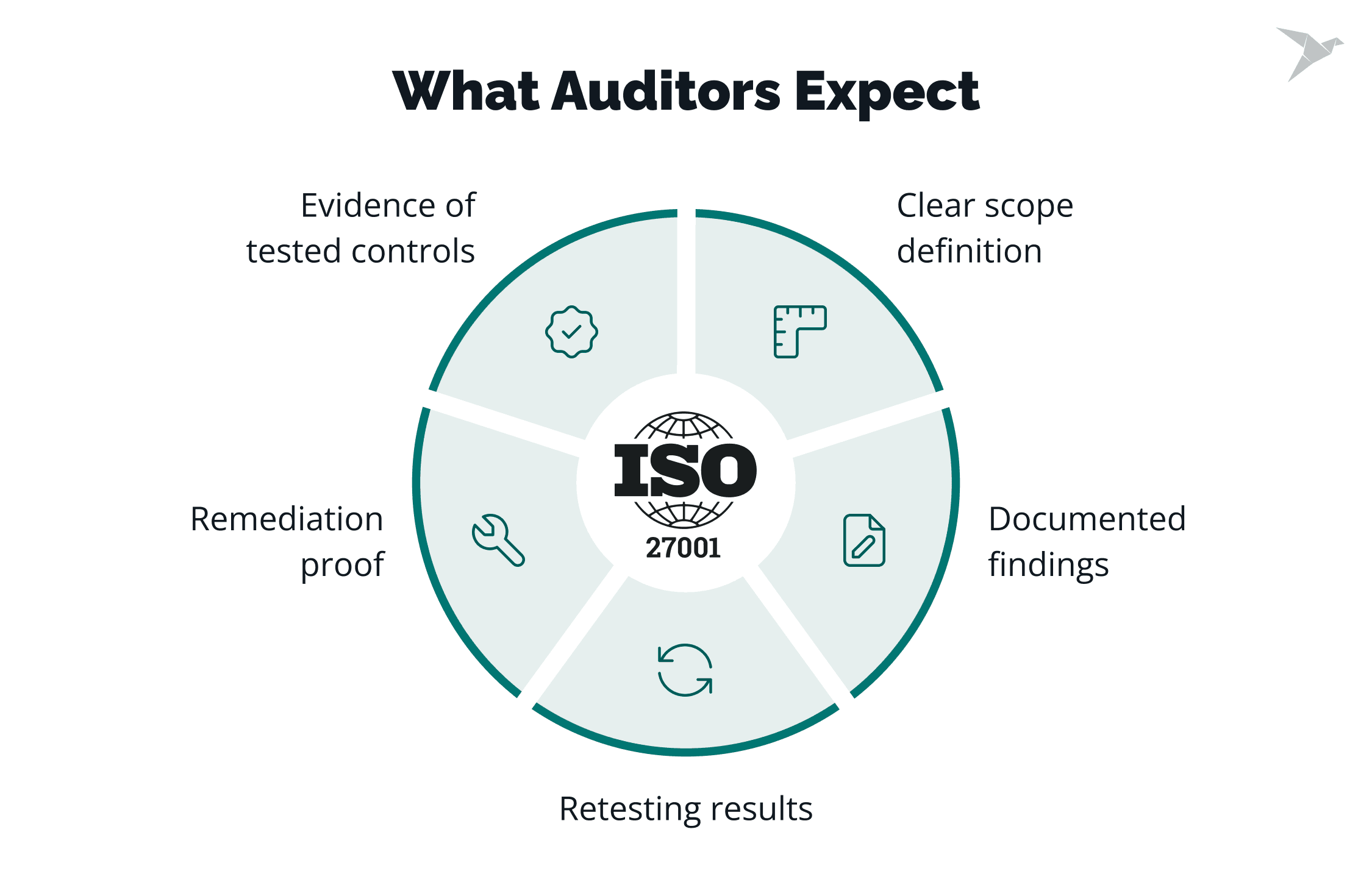
During certification audits, auditors review whether the organization can demonstrate that implemented controls are effective. They look for evidence that risks are actively managed and that safeguards are tested in a meaningful way.
For organizations that run complex applications, public-facing platforms, or high-risk infrastructure, technical validation is often expected. Testing activities such as vulnerability assessments or penetration testing can provide practical evidence that the security measures defined in the ISMS function as intended.
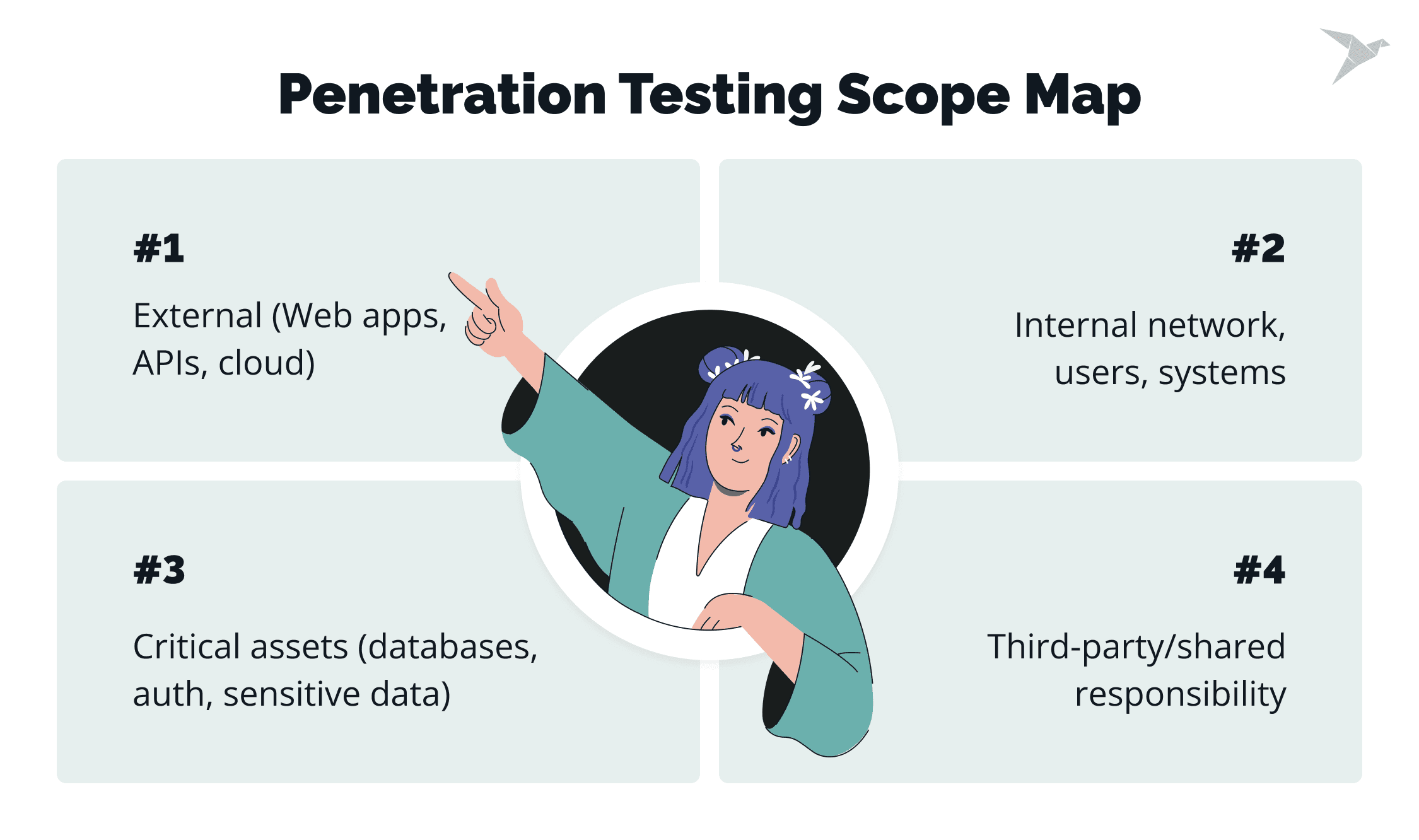
What to Include in the Scope of an ISO 27001 Penetration Test?
The scope of a penetration test should match the scope of the organization’s ISMS. This means the test focuses on systems, services, and assets that store, process, or transmit sensitive information within that defined boundary.
When planning penetration testing for ISO 27001, the goal is not to test everything blindly. The scope should reflect risk, business impact, and the real attack surface that could affect the organization or its customers. A well-defined scope also makes the results easier to explain during an audit.
Asset inventory alignment and criticality
The starting point is the organization’s asset inventory. This list helps identify areas such as systems, applications, databases, and infrastructure that support business operations.
Critical assets should receive priority. These often include systems that store sensitive customer data, authentication services, and platforms that support core business functions. Aligning the test with the asset inventory helps identify areas where security failures would have the highest impact and where the organization’s risk profile is most exposed.
External perimeter, apps, APIs, and cloud services
External-facing systems usually form the first layer of testing. These systems represent the entry points that attackers can reach from the internet.
Typical examples include public web applications, APIs, customer portals, and cloud-hosted services. Testing these assets helps determine whether external attackers could gain unauthorized access or exploit exposed services. This is often especially important for customer-facing platforms that shape trust for potential clients and support broader compliance needs.
Internal network and privileged access paths
Security testing should also consider what happens after an initial foothold is gained. Internal systems may contain additional weaknesses that allow attackers to move across the network or escalate privileges.
This part of the scope may include internal applications, directory services, or administrative interfaces. The goal is to understand whether an attacker could reach sensitive systems through internal paths, especially after significant changes to infrastructure, architecture, or access models.
Third-party components and shared responsibility boundaries
Modern systems often rely on external platforms, cloud providers, and third-party services. The scope should clearly define which components are tested directly and which fall under a shared responsibility model.
For example, infrastructure managed by a cloud provider may have limitations on what can be tested. Clear documentation of these boundaries helps ensure the penetration test remains aligned with service agreements, supports regulatory requirements, and still provides meaningful security insights. This clarity also matters when organizations need to show that security activities reflect both technical realities and formal compliance needs.
How Do You Choose the Right Type of Testing for ISO 27001 Evidence?
The right testing approach depends on one question: what do you need to prove about your security controls? As we said, within an ISMS, testing should produce clear evidence that protections work and that identified risks are properly managed. The method you choose should match the systems in scope, the level of risk, and the type of assurance auditors expect to see.
Penetration testing vs vulnerability scanning
Vulnerability scanning and penetration testing serve different purposes. A vulnerability scan automatically checks systems for known weaknesses and misconfigurations. It helps identify common issues quickly and supports regular monitoring.
Penetration testing goes further. It attempts to exploit weaknesses to show how an attacker could actually compromise a system. This approach provides stronger assurance that defenses are effective. When organizations discuss ISO 27001 pentesting, they usually mean this deeper form of validation that demonstrates how well controls hold up under realistic attack scenarios.
Black-box vs gray-box vs white-box approaches
Testing methods also differ in how much information the tester receives about the system.
A **black-box **test simulates an external attacker with no prior knowledge. This approach focuses on the exposed attack surface and shows how a real-world attacker might begin probing the system under real-world threats and possible cyber attacks.
**Gray-box **testing provides limited internal information, such as user credentials or partial documentation. This method reflects scenarios where attackers gain some level of access before attempting deeper exploitation.
**White-box **testing gives full visibility into the system’s architecture, code, and configuration. This approach is often used when the goal is to examine complex applications or internal systems in detail, often alongside code reviews to uncover deeper potential weaknesses.
Web/API, mobile, network, cloud configuration testing
The testing format should also match the technology in scope. Web applications and APIs often require focused security testing to uncover authentication flaws, data exposure, logic errors, or issues such as SQL injection. Mobile applications introduce their own risks, such as insecure storage or unsafe communication with backend services.
Infrastructure testing may focus on internal networks, identity systems, or cloud environments. In cloud-based systems, configuration errors and permission issues can create serious risks. Choosing the right testing focus helps ensure the assessment reflects the organization’s real attack surface and supports broader compliance requirements.
Retesting and validation after remediation
Testing does not end once vulnerabilities are identified. Fixes should be verified to confirm that the issue is fully resolved and that no new weaknesses were introduced.
This validation step is important because threats evolve, and a fix that looks complete on paper may still leave gaps in practice. Retesting also helps teams produce a final report with valuable data about what was resolved, what still needs attention, and how the system stands up to current risks.
That kind of evidence is especially useful for organizations aligning their security efforts with standards from the International Organization for Standardization and preparing for future audits.
Retesting provides evidence that remediation actions were effective. This step also helps organizations understand how improvements reduce risk over time and supports clearer planning for security investments, including decisions related to ISO 27001 cost and ongoing assurance activities.
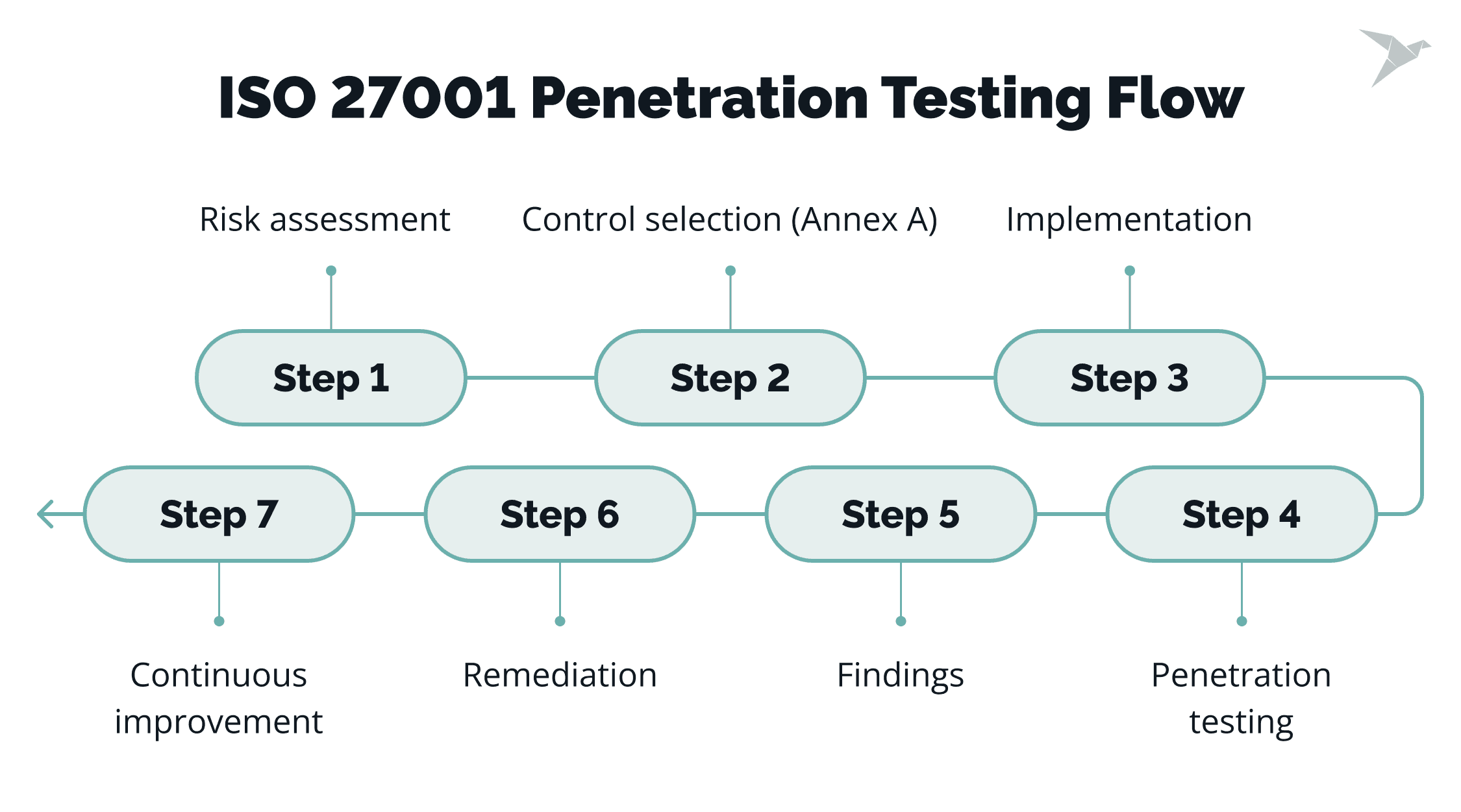
When Should You Run Penetration Testing During an ISO 27001 Implementation?
From our experience, timing really matters. If testing happens too early, the system may still be changing, and the results will quickly become outdated. If it happens too late, there may not be enough time to fix issues before the certification audit. The most useful approach is to align testing with key ISMS milestones and system stability.
Pre-certification baseline testing
A baseline penetration test is usually performed after the ISMS scope is finalized and the main security controls are already in place. At this stage, systems, infrastructure, and processes should be relatively stable.
The goal of this assessment is to validate that implemented protections work as expected. The results help identify gaps that need remediation before the certification audit. When we run pentesting ISO 27001 activities at this point, it allows the organization to demonstrate that technical controls were tested and improved before formal evaluation.
Testing after major changes and releases
Security posture changes whenever systems change. New features, infrastructure updates, migrations, or architecture modifications can introduce new risks.
Testing after major releases or structural changes helps confirm that security controls still function correctly. This approach prevents previously fixed vulnerabilities from returning and ensures that new components do not introduce weaknesses.
Recurring cadence for surveillance and continuous improvement
ISO 27001 expects ongoing improvement rather than one-time validation. After certification, organizations continue to review risks and verify that controls remain effective.
Regular security testing supports this process. Scheduled assessments help track how the environment evolves, confirm that remediation efforts remain effective, and provide fresh assurance evidence during surveillance audits.
How to Choose the Right Penetration Testing Vendor for ISO 27001
A penetration testing vendor should understand how security testing fits into an Information Security Management System. They must not only find vulnerabilities but also produce evidence that security controls work in practice.
They should also document testing results in a way that auditors can review easily. Clear reports, structured findings, and practical remediation steps help organizations show that testing supports risk management and aligns with ISO 27001 penetration testing guidance.
Proven expertise and recognized certifications
A reliable vendor should demonstrate proven experience and follow recognized testing standards. Certifications and industry accreditations indicate that testing methods meet professional security requirements.
TechMagic’s security team holds CREST accreditation. This confirms that our penetration testing practices follow internationally recognized standards and are performed by qualified specialists.
Experience with regulated and security-sensitive industries
Security expectations are higher in industries such as healthcare, finance, and platforms that handle sensitive data. Vendors with experience in these environments understand complex systems, compliance pressures, and the importance of clear risk reporting.
TechMagic has more than 11 years of experience delivering secure software solutions across HealthTech, FinTech, and other security-focused sectors.
Practical experience with ISO frameworks
It also helps when a vendor has firsthand experience with ISO security frameworks. TechMagic has successfully passed its own ISO audit, which means our internal processes, documentation, and controls were evaluated against the same framework many clients are implementing.
This experience allows our team to connect penetration testing with broader ISO 27001 consulting services and help organizations strengthen security controls, prepare for certification, or improve their ISMS over time.
Final Thoughts
ISO 27001 asks organizations to build a security program that can be explained, justified, and verified. In this context, penetration testing helps demonstrate that technical controls work in real conditions and that security risks are reviewed in a practical way.
Penetration testing is most useful when it matches the scope of the ISMS and focuses on the systems that matter most. That usually includes critical assets, exposed services, and areas where a security failure would have the highest business impact. The value of any ISO 27001 penetration testing requirement depends on how well the organization connects testing results to risk treatment, assurance, and remediation.
What matters most in practice
A useful testing process starts with a clear scope. From there, the organization selects the method that fits its risks, environment, and audit goals. That may include black box testing, targeted validation, or broader vulnerability analysis, depending on the systems in scope. Timing also matters. Testing should happen when systems are stable enough to be assessed properly and early enough to leave room for remediation before the audit.
This makes penetration testing part of ongoing security management rather than a one-time security assessment. It helps teams validate information security controls, confirm priorities in the risk register, and show that security work reflects real conditions.
In that sense, it becomes an essential component of a more comprehensive framework for managing security vulnerabilities and responding to emerging threats. It also supports the kind of evidence that auditors expect evidence for during an internal audit or external review.
2025–2026 numbers that shape the conversation
The pressure on security teams is increasing. IBM’s 2025 Cost of a Data Breach Report puts the global average breach cost at $4.4 million. The same report found that 63% of organizations lacked AI governance policies, and 97% of organizations that reported an AI-related security incident lacked proper AI access controls.
The certification landscape is also becoming more standardized. ISO states that from 2025, the ISO Survey is compiled directly from anonymized data in IAF CertSearch to provide a more complete view of accredited certifications worldwide.
For organizations working to achieve compliance with existing information security standards, this makes technical proof even more important. It is no longer enough to rely only on policy documents or automated tools. Teams need secure testing and a defensible security assessment approach that helps protect systems, support data protection, and expose security vulnerabilities before they turn into real incidents.
What to expect next
The 2026 outlook points to more complexity for security teams. The World Economic Forum says cyber risk is being shaped by faster AI adoption, geopolitical fragmentation, and widening gaps in cyber capability. Google Cloud’s Cybersecurity Forecast 2026 adds that attackers are increasingly using AI in routine operations, including social engineering and attacks on AI systems. Check Point Research also expects AI to accelerate familiar attack patterns through faster reconnaissance and more convincing deception.
For ISO 27001 programs, this raises the importance of technical evidence. Organizations will need to show that controls are selected based on risk, tested in the right places, and reviewed often enough to keep pace with change.
Penetration testing remains useful because it gives both auditors and internal teams a clear way to evaluate how systems perform under realistic attack conditions and against evolving cyber threats. It helps strengthen information security controls, uncover security vulnerabilities, and provide a more grounded security assessment of how well defenses hold up in practice.
We’re here to make sure your business stays secure and meets the standards

FAQ

ISO 27001 does not explicitly require penetration testing. The standard requires organizations to demonstrate that security controls are effective and aligned with identified risks, especially when demonstrating compliance during audits.
In practice, many organizations perform regular penetration testing because it helps identify vulnerabilities and provides strong technical evidence that controls work in real conditions. Whether it is used depends on the organization’s risk assessment, ISMS scope, and the controls listed in the Statement of Applicability. Some teams also use external penetration testing services to validate security from an independent perspective.
Several Annex A controls connect to technical security testing. The most relevant areas include vulnerability management, technical vulnerability identification, secure system development, and monitoring of information systems.
These areas matter because penetration testing can reveal security weaknesses that are harder to detect through routine checks alone. It can also support continual improvement by helping organizations refine controls over time.
Penetration testing helps validate that these controls work as expected. For example, assessments such as ISO 27001 network security penetration testing can help verify that exposed systems, authentication mechanisms, and internal network protections are configured and operating securely.
Not completely. Vulnerability scanning and pen testing serve different purposes. A vulnerability scan automatically detects known weaknesses such as outdated software or configuration issues. Penetration testing goes further by attempting to exploit weaknesses and evaluate how an attacker could move through the system.
For many environments, both methods are useful. Vulnerability scanning supports technical vulnerability management, while penetration testing provides deeper assurance that security controls can withstand realistic attack scenarios and help protect sensitive data. Because penetration testing involves validation in real-world conditions, it also requires strong technical expertise to assess risk accurately and interpret the findings in context.

















 TechMagic Academy
TechMagic Academy





