Why Compliance Software Isn’t Enough for Successful Audit
Last updated:10 March 2026
Many teams invest in compliance monitoring tools expecting clarity and control. They map frameworks, collect evidence, and track tasks. On paper, everything looks structured. Yet audits don’t evaluate how well your dashboard is configured. They assess whether controls actually work: consistently, over time, with clear ownership and traceable proof.
And here is the gap. Compliance software improves visibility, supports compliance monitoring, reduces manual effort, and centralizes documentation. It can also give teams a clearer view of their compliance status. However, it does not design your controls, enforce accountability, or ensure that daily operations match written policies and broader regulatory compliance goals.
In our new article, we’ll break down what compliance monitoring software in cybersecurity really does, why teams often overestimate its impact, where operational gaps hide, and how to build a compliance model that stands up to real audit scrutiny and actual compliance requirements.
Key takeaways
- Compliance software improves organization, evidence collection, and operational efficiency, but it does not implement or enforce controls.
- Audits evaluate how controls operate in practice, not how complete your documentation looks or how much activity your compliance efforts appear to cover.
- The most common gaps appear in daily operations such as access management, vendor risk reviews, incident response, and change control.
- Sustainable compliance depends on defined ownership, repeatable processes, and consistent execution over time.
- A compliance tool should scale a working governance model, yet you still need a substitute for accountability or leadership oversight.
- An effective compliance monitoring plan ensures that organizations have the provisions and people in place to secure their sensitive information. Yet, establishing a program that did not exist before requires new resource allocation, and often new allowances of staff, budget, and time.
What Are Compliance Tools in Cybersecurity?
Compliance tools in cybersecurity are software platforms that help organizations manage and document their adherence to security standards, legal obligations, and internal rules. They support continuous compliance by giving teams a more structured way to track controls, collect evidence, and align daily work with relevant compliance standards.
They also centralize activities and help with automating manual compliance tasks that would otherwise require spreadsheets, reminders, and manual follow-up.
Automated workflows in compliance monitoring tools streamline key compliance processes, including gifts and hospitality, anti-bribery and corruption, and conflicts of interest. These features also help teams monitor compliance more consistently across different departments and systems.
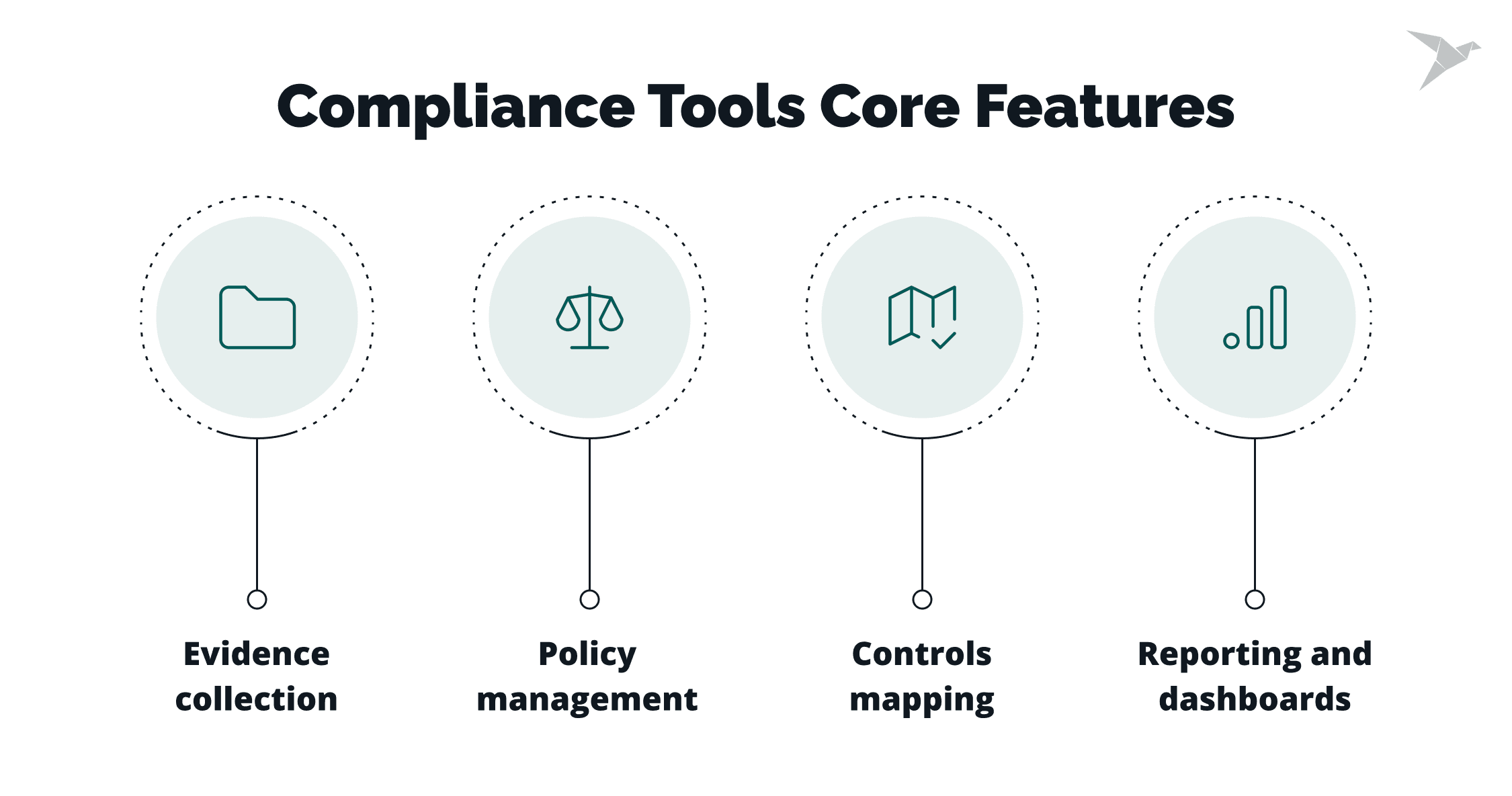
Most tools support four core areas:
- Evidence collection. They gather logs, configurations, and activity records from cloud platforms, identity providers, ticketing systems, and code repositories. This helps teams prepare audit-ready evidence without chasing screenshots and exports.
- Policy management. Many platforms provide policy templates aligned with frameworks such as ISO 27001, SOC 2, HIPAA, or GDPR. Teams can adapt these templates to their environment and track policy reviews and approvals.
- Controls mapping. A compliance monitoring tool often maps technical and organizational controls to multiple frameworks at once. This reduces duplicate work when a company needs to meet more than one standard.
- Reporting and dashboards. Tools generate status reports, highlight control gaps, and track remediation progress. This gives leadership and auditors a clear view of compliance posture over time.
These platforms improve visibility and reduce manual effort. They create structure around complex requirements and help teams stay consistent.
Compliance monitoring software can build a centralized compliance library with relevant regulations, standards, internal policies, and procedures. It can also support continuous monitoring and make it easier to maintain compliance as systems, risks, and audit expectations change.

Why Do Teams Assume Compliance Tools Automatically Make Them Compliant?
In practice, many teams make this assumption because they are under pressure to pass audits, satisfy customer security reviews, and support sales conversations. In that setting, buying software feels like a fast and measurable step toward meeting regulatory compliance requirements, aligning with industry standards, and addressing growing industry regulations.
This often leads to checkbox behavior, where the focus moves from building a working security program to completing tasks in a platform.
"We bought the tool, so we’re covered" mindset
Many teams assume that once a platform is in place, the organization can ensure compliance with the required standard. The purchase itself starts to look like proof of maturity.
In reality, tools provide structure and visibility. They do not design controls, assign accountability, or guarantee consistent execution. Without defined owners and clear processes, tasks inside the system can stay incomplete or outdated. The tool records activity, but it does not prove that controls work as intended.
This mindset often appears when leadership wants a clear signal that compliance is handled. The platform becomes that signal, even when the underlying governance is still evolving.
Confusing documentation with real security
Compliance requires documentation. Tools make this easier by offering templates, centralized storage, and mapped controls. That efficiency can create a false sense of security.
Well-written policies do not mean employees follow them.
Uploaded evidence does not confirm that access reviews or incident response procedures happen regularly.
When teams focus on filling folders and closing checklist items, they can miss whether controls are effective in practice. Auditors and customers expect documented proof, but mature security programs also depend on consistency, ownership, and operational discipline. This is where risk and compliance must work together. Documentation supports security, but it does not replace it.
Compliance as a sales requirement
For many growing companies, compliance starts as a sales requirement. A prospect asks for SOC 2 compliance or ISO 27001 alignment, and the deal depends on it. The initiative becomes deadline-driven and audit-focused.
Under this pressure, monitoring tools for compliance are positioned as a quick way to “get certified.” The goal shifts to passing the audit instead of building a long-term security model. When compliance lives only in the GRC tool and not in daily engineering and operational workflows, gaps appear after the audit window closes. Controls weaken, reviews slow down, and ownership becomes unclear.
Compliance works best when treated as an operating model that shapes how teams design systems, manage access, and respond to incidents.
Overreliance on automated scoring dashboards
Dashboards provide status indicators, risk scores, and control coverage metrics. These views are useful for tracking progress and identifying gaps.
Problems arise when teams treat a high score as confirmation of full compliance. Automated checks typically cover technical configurations and integrations. They cannot assess culture, training quality, or whether people follow procedures under real pressure.
A green dashboard can hide weak processes behind the scenes. Leaders may rely on summary metrics without validating how controls perform in daily operations.
What Does "Being Compliant" Actually Mean Beyond Using a Tool?
Being compliant means running a consistent system of controls, ownership, and verifiable evidence over time. It is an ongoing process that supports daily business operations, not a one-time setup in a platform. Compliance software tools can help organize work, but real compliance depends on how well the organization runs its compliance program and adapts it to regulatory changes.
It’s not enough to map controls; they must be implemented
Mapping controls to a framework is only the starting point. Real compliance requires those controls to be designed, implemented, and tested in live environments. This is where a practical compliance strategy matters. It connects documented controls to real compliance activities and makes sure they work in practice.
For example, access reviews must happen on schedule. Logging must be enabled and monitored. Incident response procedures must be exercised and updated. A control listed in a platform does not reduce risk unless it operates consistently and produces results. A strong compliance monitoring program or compliance management solution can support that work, but it cannot replace execution.
Framework alignment shows intent. Implementation shows execution.
Policies must reflect reality, not templates
Policy templates help teams structure documentation quickly. However, policies that do not match actual workflows create risk.
If a policy states that privileged access is reviewed monthly, the review must occur monthly and the process must be traceable. When documentation describes an ideal state that differs from daily practice, findings in compliance audits become more likely. Effective compliance requires policies that reflect how the organization truly works. When processes change, documentation must change with them.
Evidence must be continuous and verifiable
Auditors look for proof that controls function over time. Screenshots taken the week before an audit rarely demonstrate consistency.
It is important to generate evidence as part of normal operations: system logs, approval records, change tickets, and review reports. These artifacts must be timestamped, attributable, and retained according to defined retention rules. This is also where automated compliance monitoring can help. It supports evidence collection, reduces the risk of missed actions, and lowers the chance of legal penalties caused by poor documentation or weak execution.
Organizations that treat compliance as part of how they operate are in a stronger position. They reduce risk, respond faster to change, and often gain a real competitive advantage.
One of the cons of compliance monitoring tool reliance is the assumption that automated evidence collection alone proves effectiveness. Automation supports traceability, but teams still need to validate that collected data represents meaningful control activity.
Responsibilities and approvals must be clear
Compliance frameworks require defined roles and documented approvals. Each control must have an owner responsible for execution and oversight.
Policy updates, risk acceptances, access grants, and other approval workflows need to be formalized and recorded. Unclear ownership leads to delayed and overlooked tasks. When approvals are informal, audit trails weaken.
Clear responsibility structures create accountability, and accountability makes compliance sustainable.
Penetration testing of a cloud-native hospital management system before the annual ISO 27001 audit
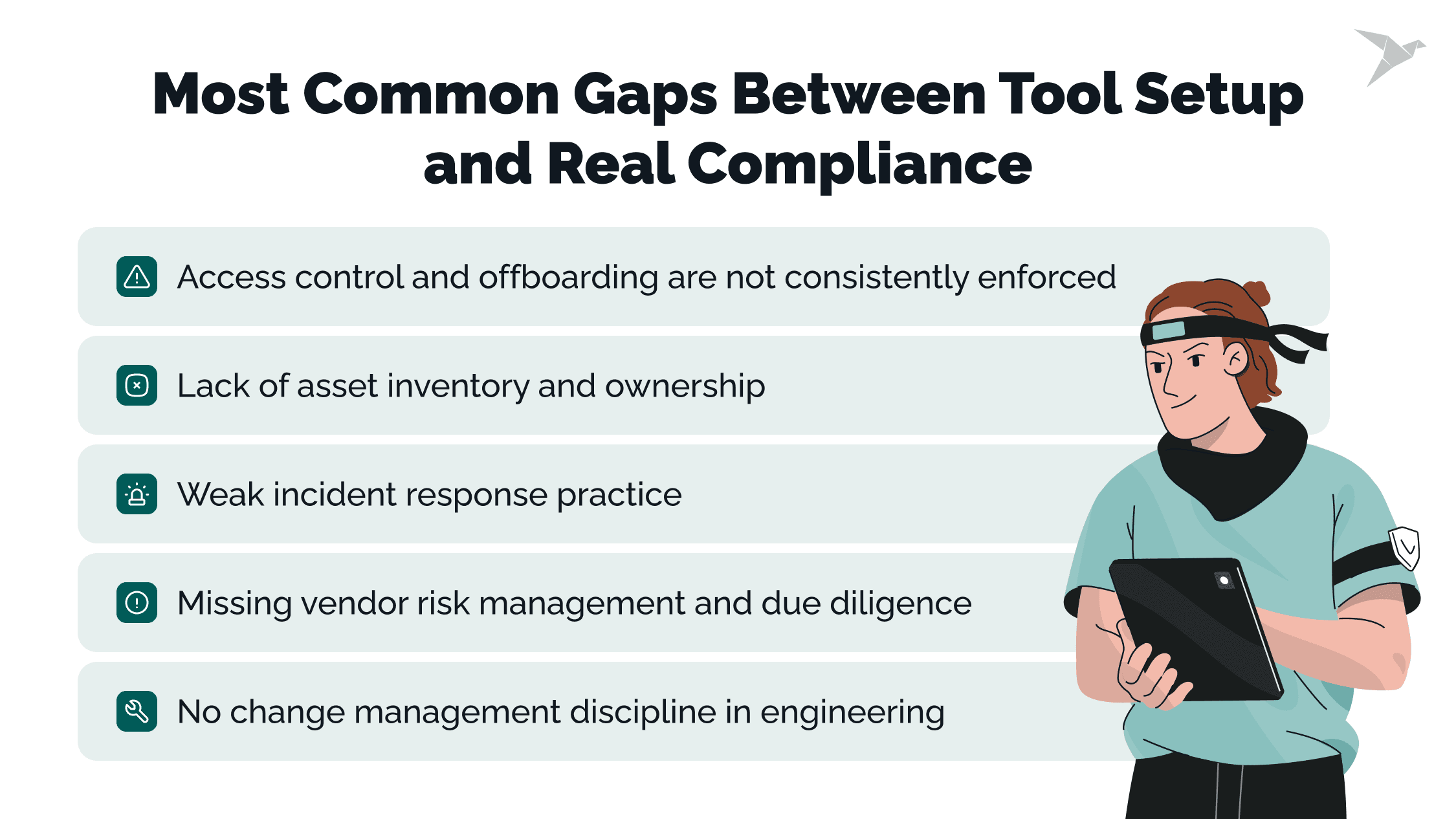
What Are the Most Common Gaps Between Tool Setup and Real Compliance?
The most common gaps show up in day-to-day operations, even when a tool is fully configured. In our work, we often see teams move fast on automation, then get surprised by what auditors and customers still flag.
Access control and offboarding are not consistently enforced
Tools can surface accounts and permissions, but they cannot force timely offboarding or careful access reviews. We often see delayed deprovisioning, over-permissioned users, and reviews marked “done” without clear approvals.
Lack of asset inventory and ownership
Integrations can pull cloud and endpoint data, yet inventories still miss shadow systems. Customers and auditors keep asking: who owns this asset, what data it handles, and is it in scope?
Weak incident response practice
A stored IR plan does not prove readiness. We regularly see missing evidence of tabletop exercises, runbooks that are not used, and no documented lessons learned. This is one of the drawbacks of monitoring tools for compliance: they track artifacts, not performance under pressure.
Missing vendor risk management and due diligence
Vendor lists and questionnaires help, but due diligence often stays inconsistent. We commonly find incomplete risk assessments, unclear approval criteria, and no schedule for reassessments. That’s a key part of the cons of tools for compliance when teams expect the workflow to run itself.
No change management discipline in engineering
Compliance platforms do not create an engineering discipline. We often see production changes without consistent peer review, ticket links, or approvals. This is where the tool looks "green," but the audit trail is thin.
How Do You Make Regulatory Compliance Sustainable With or Without a Tool?
The best way to make compliance sustainable is to build clear controls, ownership, and repeatable internal processes first. Only after that should tools be added to scale and simplify the work.
The sequence matters more than the software. Teams that focus on fundamentals before automation usually move faster during reviews, improve audit readiness, and protect data security more consistently over time.
Start with a clear scope and risk assessment
Define what systems, data, and teams are in scope. Identify which regulations or standards apply, then assess where the real exposure sits. Without that clarity, control design becomes guesswork. A tool cannot fix a poorly defined boundary or misaligned priorities.
Implement core controls before automation
Put core controls in place first: access management, logging, backups, incident response, change management, and vendor review. Assign owners and define how often each control runs.
These controls need to work in daily operations before automation is added. If a process fails manually, automation often hides the weakness instead of solving it. Teams should also conduct regular audits to confirm that controls are working as expected.
Build repeatable processes and ownership
Document how controls operate, who approves them, and where evidence is stored. Set review cycles and escalation paths. Compliance becomes sustainable when responsibilities are clear and recurring work is scheduled. This reduces reliance on memory and makes compliance-related tasks easier to manage.
Defined ownership and cross-team coordination often matter more than any platform feature. They also make it easier to produce detailed reports when auditors or customers ask for proof.
Use tools to scale, not to substitute
Once controls and processes are working, tools can help centralize evidence, track deadlines, and monitor gaps. That is where compliance monitoring software work becomes useful in practice. It supports visibility, reduces manual effort, and helps teams stay organized.
Sustainable compliance comes from disciplined execution. Tools can support that model, but they do not replace governance or accountability. When these basics are in place, organizations are better prepared to avoid legal penalties and keep compliance stable as the business grows.
We Already Have a Compliance Application, So We No Longer Need Consultants to Prepare for Audits, Right?
A compliance application helps organize work. Yet, someone still needs to manage and supervise the audit preparation process.
A system may be in place, but no one actively controls implementation, validates that controls operate as designed, or reviews whether evidence is complete and consistent. Tools collect data, and they DO NOT challenge gaps, follow up with control owners, or assess whether documentation reflects reality. This becomes critical for ISO 27001 compliance, NIST compliance, or other cybersecurity frameworks, where auditors expect structured oversight and clear accountability.
There is also a practical constraint: your teams already have full workloads. Engineering, DevOps, HR, and security leads focus on delivery and operations. Adding audit preparation on top of daily responsibilities often leads to delays, incomplete evidence, or rushed reviews.
When someone with hands-on audit experience manages the process, preparation becomes structured and predictable. They track deadlines, review evidence before the auditor sees it, and address any gaps early. This is where external cybersecurity compliance services can provide value. Experts don’t have to replace your internal team, but they can coordinate efforts, validate readiness, and reduce disruption.
So, a compliance platform supports the workflow; a responsible lead ensures the organization is truly prepared.
Final Thoughts
Compliance tools help teams centralize evidence, map controls, support compliance tracking, and generate dashboards. They reduce manual effort and contribute to enhancing operational efficiency. At the same time, they do not implement controls, enforce accountability, or confirm whether processes work under real conditions or align with external regulatory requirements and broader regulatory requirements.
We often see the same situation: the platform looks complete, but gaps remain in access management, asset ownership, incident response, and change control. In these cases, strong compliance management depends less on dashboards and more on whether teams can detect gaps early, respond to compliance violations, and understand the true organization's compliance status.
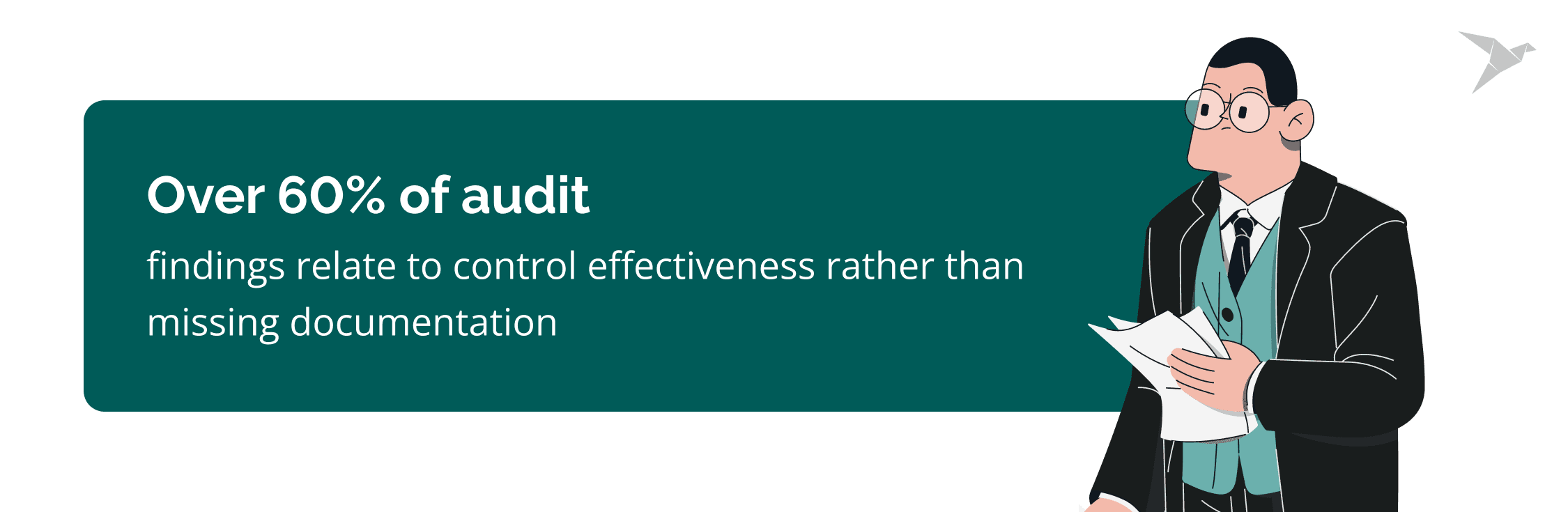
Audits are becoming more operational
Regulators and enterprise customers are asking for stronger proof of execution. In 2025, industry reports showed that more than 60% of audit findings were tied to control effectiveness rather than missing documentation. Third-party risk reviews also increased across SaaS supply chains, with vendor security assessments becoming a standard part of enterprise procurement.
Automated dashboards alone are not enough. Auditors now ask for evidence of repeated control performance over time, records of management review and approval, and proof of incident simulations and response testing. This shift favors organizations that use structured compliance workflows and practical compliance solutions to maintain ongoing compliance.
The future of compliance efforts is continuous, integrated, accountable
Looking ahead to 2026 and beyond, compliance will continue moving toward continuous assurance. Frameworks are aligning more closely with real-time monitoring, structured risk management, and clear accountability. AI can support evidence review, but ownership still stays with people.
We can support you at every stage of this shift. Our team helps you prepare for audits, structure evidence, and align controls with regulatory expectations before issues surface. If additional tools are needed, we can help you choose the right ones for your environment and avoid unnecessary spending.
Instead of second-guessing or overspending, you get a compliance program that’s practical, efficient, and ready to scale.

FAQ

No, compliance tools do not guarantee certification. They help organize documentation, map controls, and collect evidence across different regulatory frameworks and compliance regulations. They can also support tasks such as vendor compliance checks and help teams document alignment with applicable regulations and regulatory standards.
Certification depends on whether controls are properly designed, implemented, and operating over time. Auditors look at effectiveness, consistency, accountability, and how the organization manages its compliance obligations in practice. A platform can support preparation, but it cannot prevent compliance breaches or replace governance, management review, or operational discipline.
Companies fail audits because tools track activity, but they do not ensure that controls work in practice. Common issues include incomplete access reviews, weak vendor assessments, untested incident response plans, and unclear ownership. These gaps often reflect the cons of compliance tool reliance when teams assume configuration equals readiness.
Another factor involves the drawbacks of compliance monitoring tool dependence. Automated checks focus on technical signals and integrations. They rarely measure process quality, staff awareness, or whether procedures are followed consistently under real conditions. Audits test execution.
Compliance means meeting defined regulatory or framework requirements through documented controls, compliance policies, and evidence. Security means protecting systems and data from real threats.
Compliance provides structure through controls, policies, evidence, and document management. It also often relies on manual processes and automated alerts to track gaps and flag compliance issues before they grow into regulatory non-compliance.
Security focuses on reducing risk in a changing threat landscape. An organization can be compliant but still insecure if controls exist on paper and are not effective. Strong security practices often support compliance, but compliance alone does not guarantee resilience.

















 TechMagic Academy
TechMagic Academy