How to Create a GDPR-compliant EMR Without Slowing Down Development?
Last updated:14 April 2026
Every 24 hours, a hospital somewhere in Europe faces a data breach. Healthcare is the single most targeted industry for cyberattacks globally, and EMR systems sit right at the center of that bullseye, holding the most sensitive data a person can have.
If you're thinking about how to create a GDPR-compliant EMR, GDPR is the foundation. Get it wrong, and you're looking at fines up to €20 million and systems that regulators can force offline. Get it right from the start, and you build something that's secure, scalable, and resilient without constantly retrofitting compliance on top of fragile architecture.
In our new GDPR EMR creation guide, we discuss what makes health data a "special category", which security controls are non-negotiable under GDPR, and where most systems fail. We also describe the exact steps to build or validate a compliant EMR, as well as legal and operational requirements that get overlooked even by experienced teams.
Key takeaways
- Health data falls under GDPR Article 9 as a special category, triggering stricter obligations than standard personal data. Your EMR must reflect this from day one.
- GDPR compliance means data privacy and security are built into the architecture. The most common failures, like weak access control, poor audit logging, and insecure third-party integrations, are all preventable with the right planning.
- Compliance is ongoing. Continuous monitoring, staff training, and tracking your compliance status over time turn good intentions into a defensible record.
- Patient requests must be handled within one month, data retention policies must be clearly defined, and the relevant supervisory authority must be notified within required timeframes in the event of a breach.
- All third-party vendors must sign Data Processing Agreements. Where data crosses borders, implement standard contractual clauses: maintaining patient trust across all healthcare operations depends on getting these foundations right.
What is a GDPR-compliant EMR?
An Electronic Medical Record system is a digital version of a patient’s medical history. It stores data such as diagnoses, medications, treatment plans, test results, and clinician notes. Healthcare providers use EMRs to document care, track patient progress, and support clinical decisions.
Because EMRs handle sensitive health information, they fall under strict data protection rules in the European Union. A GDPR-compliant EMR is a system designed to process patient data in line with the General Data Protection Regulation. The GDPR defines health data as a special category of personal data. This means it requires a higher level of protection than standard personal information like names or email addresses.
Learn about our expertise and sign up for a free consultation

Why Does GDPR Affect EMR System Development?
In two words, healthcare data is among the most sensitive types of personal data under the regulation. This creates stricter legal obligations and higher risks if something goes wrong. As a result, GDPR-compliant EMR development must account for privacy, security, and accountability from the start.
Health data as a special category of personal data
Under GDPR (Article 9), health data is classified as a special category of personal data. This includes any information about a person’s physical or mental health, including medical history, diagnosis, and treatment.
Processing this type of data is generally prohibited unless specific conditions are met. For example, it may be allowed for medical diagnosis, healthcare provision, or public health purposes. Even in these cases, organizations must apply additional safeguards to protect the data.
For EMR systems, this means stronger protection is a legal requirement tied directly to the nature of the data.
Data controllers vs data processors in healthcare systems
GDPR defines two key roles: data controllers and data processors (Article 4).
A data controller decides why and how personal data is processed. In healthcare, this is often a hospital, clinic, or healthcare provider.
- A data processor handles data on behalf of the controller. This can include software vendors or cloud service providers that operate the EMR system.
- Both roles have clear responsibilities. Controllers must ensure lawful processing and protect patient rights. Processors must follow the controller’s instructions and implement appropriate security measures (Article 28).
In practice, a GDPR-compliant EMR system must support these roles. It should allow clear control over data access, processing activities, and responsibility boundaries.
Regulatory penalties for GDPR violations
GDPR includes strict penalties for non-compliance (Article 83). Organizations can face fines of up to €20 million or 4% of global annual turnover, whichever is higher.
The level of the penalty depends on factors such as:
- The severity of the violation.
- Whether it was intentional or due to negligence.
- The type of data involved, including whether it was sensitive health data.
For EMR systems, this creates a strong incentive to build secure and compliant solutions. Failures in data protection can lead not only to financial loss but also to legal action and operational disruption.
Trust and patient privacy expectations
GDPR also reflects expectations around patient privacy and trust. Patients expect their medical data to remain confidential and protected from unauthorized access. GDPR reinforces this by requiring transparency (Articles 12–14) and giving individuals rights such as access to their data and information about how it is used.
If an EMR system fails to protect patient data, the impact goes beyond regulation. It can damage trust between patients and healthcare providers, which is essential for effective care. For this reason, GDPR shapes both the technical and ethical foundations of EMR system design.
What Security Requirements Must a GDPR-Compliant EMR Implement?
To protect patient data under GDPR, an EMR system must ensure confidentiality, integrity, and availability of information. This means preventing unauthorized access, keeping data accurate, and making sure it is available when needed. If you are thinking about how to build a GDPR-compliant EMR, these security controls are essential.
Identity and access management for healthcare users
You need to control who can access the system and what they can do. This includes strong authentication methods, such as multi-factor authentication, and role-based access control.
For example, a doctor may access full patient records, while administrative staff may only see scheduling data. Access should be limited to what each user needs to perform their role.
Encryption of patient data at rest and in transit
Patient data must be protected both when stored and when transmitted. Encryption at rest protects data stored in databases or backups. Encryption in transit protects data moving between systems, such as between an EMR and a lab system. This helps prevent interception or unauthorized access.
Secure logging and audit trails
The system should record key actions, such as who accessed a record, what changes were made, and when. Audit logs help detect suspicious activity and support investigations if something goes wrong. They also help demonstrate compliance during audits.
Secure APIs and integration security
EMRs often connect with other systems, such as billing platforms or diagnostic tools. These integrations must be secured. APIs (Application Programming Interfaces) should require authentication, validate inputs, and limit access. Without proper controls, integrations can become entry points for attacks.
Backup, disaster recovery, and system resilience
You need to ensure that data is not lost and systems remain available. Regular backups protect against data loss. Disaster recovery plans help restore systems after incidents such as cyberattacks or system failures. Resilience measures, such as redundancy, reduce downtime and ensure continuity of care.
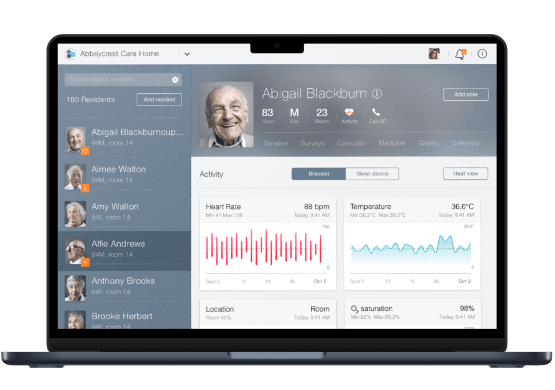
a Care home management app for E-type Care
What Steps Are Required to Create a GDPR-Compliant EMR?
Building or updating an EMR system under GDPR is a structured process. You need to understand how data is used, reduce risks, and implement controls that protect patient information. This GDPR-compliant EMR creation guide outlines the key steps you should follow.
Map healthcare data flows and identify personal data processing
Start by getting a clear picture of how data moves through your system. Conduct a thorough data mapping exercise to identify what personal data you collect, where it comes from, how it is used, and who can access it. Building a reliable data inventory at this stage helps you see potential risks and ensures transparency in data processing activities.
Conduct a data protection impact assessment (DPIA)
A Data Protection Impact Assessment (DPIA) is required when processing sensitive data like health records, including research data gathered for public interest purposes. It helps you evaluate risks to patient privacy and define measures to reduce those risks. You should document the purpose of processing, potential impacts, and safeguards you plan to implement.
Design secure architecture and access controls
Plan your system with security in mind from the start. Define how users will access the system and what permissions they will have. Use role-based access control to limit exposure of sensitive data. Ensure that only authorized users can view or modify patient records.
Implement encryption and secure storage
Protect data both in storage and during transmission. Use encryption to secure databases, backups, and communication between systems. Store data in secure environments with restricted access and clear control policies.
Build audit logging and monitoring mechanisms
- Track how data is accessed and used.
- Detailed audit trails should record actions such as logins, record access, and changes to patient data.
- Monitoring tools can help detect unusual behavior and respond quickly to potential incidents.
Implement patient consent and rights management
GDPR gives patients control over their data and your system must support this. Robust consent management features allow you to handle patient permissions clearly and consistently. You should be able to provide access to records, and handle requests for correction or deletion where applicable. These features are essential for compliance.
Perform security testing and compliance validation
Before deployment, test your system thoroughly. Working through a GDPR compliance checklist at this stage ensures that organizations collect, process, and store such data in line with regulatory requirements. This includes:
- security testing;
- vulnerability assessments;
- validation of GDPR requirements.
Regular reviews after launch help maintain compliance as the system evolves.
If you are planning how to develop a GDPR-compliant EMR, these steps provide a practical path from early planning to ongoing compliance.
What Common Mistakes Make EMR Systems Non-Compliant with GDPR?
What we see in practice is that many compliance issues in healthcare systems come from avoidable design and operational gaps. These mistakes often happen when security and privacy are treated as secondary concerns. If you are planning how to create a GDPR EMR, it helps to understand where others go wrong.
Mistake 1. Collecting or storing unnecessary patient data
One of the most common issues is collecting more data than you need. GDPR requires data minimization, which means you should only collect data necessary for a specific purpose. In practice, some systems store full patient histories, duplicate records, or unused data fields without clear justification.
This increases risk. The more data you store, the more you must protect. To prevent this, define clear data requirements and regularly review what you store.
Mistake 2. Weak identity and access management
Poor access control can expose sensitive health data to the wrong people. This often happens when all staff have broad access or when authentication is too simple. For example, shared accounts or weak passwords make it difficult to track responsibility and prevent misuse.
A secure system limits access based on roles and uses strong authentication methods. This is critical whether you build an EHR or EMR system.
Mistake 3. Lack of audit logs and monitoring
Everything is simple and plain here. Without proper logging, you cannot see how data is used or detect suspicious activity. Some systems either do not log actions or store logs in a way that is hard to review. This creates blind spots during incidents and makes compliance verification difficult.
To avoid this, implement clear audit trails and monitoring tools that track access and changes to patient data.
Mistake 4. Insecure third-party integrations
EMR systems often connect to external services such as labs, billing platforms, or analytics tools. Obviously, if these integrations are not secured, they can introduce vulnerabilities. For example, weak API protection or unclear responsibility between vendors can lead to data leaks. You should carefully assess third-party providers, define responsibilities, and secure all data exchanges.
These mistakes often reflect gaps in planning and governance. Addressing them early can reduce risks, protect patient data, and avoid unnecessary EMR cost linked to compliance failures or penalties.
What Operational and Legal Requirements Are Often Overlooked in GDPR-Compliant EMR Systems?
Building a secure system is only part of GDPR compliance. You also need clear processes, legal justification, and ongoing oversight. The following areas are often missed but are critical in real-world healthcare environments.
Define a lawful basis for processing health data
GDPR does not allow you to process health data by default. You must have a valid legal basis.
In healthcare, this is often tied to medical diagnosis, treatment, or public health purposes. In some cases, you may also need explicit patient consent. So, you should clearly document why you process data and ensure your system supports that purpose.
Set clear data retention and deletion rules
You cannot store patient data indefinitely. GDPR requires you to define how long data is kept and when it should be deleted or anonymized. This depends on medical, legal, and operational needs. Your EMR or custom EHR should support automated retention policies and secure deletion processes.
Prepare for data breaches and incident response
Even with strong security, incidents can happen. GDPR requires you to detect, report, and respond to data breaches. In many cases, you must notify regulators within 72 hours.
This means you need:
- Monitoring tools to detect incidents.
- A response plan with clear responsibilities.
- Processes for notifying authorities and affected individuals.
Manage cross-border data transfers
If your system stores or processes data outside the EU, additional rules apply. You must ensure that data transfers follow approved safeguards, such as standard contractual clauses. This is especially important when using cloud providers.
Maintain documentation and prove compliance
GDPR requires you to demonstrate compliance. You should keep records of:
- Data processing activities.
- Security controls.
- Risk assessments such as DPIAs.
Audit logs and documentation help you prove that your system meets regulatory requirements.
Train staff and define responsibilities
In General Data Protection Regulation compliance, people play a key role. Staff should understand how to handle patient data, follow access rules, and recognize risks. You should also define clear roles, including who is responsible for data protection decisions.
Final Thoughts
If you are thinking about how to make a GDPR-compliant EMR, the compliance should shape the system from the start. It handles highly sensitive patient data, and that is why GDPR affects product decisions, security controls, workflows, and ongoing system management. Here is the copy with all keywords incorporated naturally:
You need to know what data you collect, why you process it, who can access it, how you protect it, and how you prove compliance over time. Understanding what data collected flows through your system, including sensitive information such as mental health status, is essential to meeting obligations under the Data Protection Regulation GDPR.
This also means looking beyond core features. Access control, encryption, audit logs, retention rules, breach response, third-party integrations, and patient rights management all matter.
The ability to protect personal data across all these layers, and to support data portability when patients request it, is what separates a compliant system from a vulnerable one. If even one of these areas is weak, the whole system becomes harder to trust and harder to defend.
Future outlook
The urgency is growing. In 2025, healthcare remains one of the most targeted industries for cyberattacks. Reports show that over 30% of all data breaches globally affect healthcare organizations, and the average cost of a healthcare data breach has exceeded $10 million per incident. At the same time, data protection authorities continue to enforce GDPR actively, with fines reaching tens of millions of euros for improper handling of personal data security.
So, in 2026 and beyond, healthcare systems are expected to:
- Move toward zero-trust security models, where no user or system is trusted by default.
- Increase use of automated compliance monitoring and real-time audit tools.
- Adopt privacy-by-design as a standard, no exceptions.
- Strengthen control over third-party and cloud ecosystems, including data transfer mechanisms, where most risks now emerge
Another important shift is patient expectation. Users are becoming more aware of their data rights. They expect transparency, legitimate interests to be clearly stated, and fast responses to requests. Systems that cannot support this will struggle not only with compliance but also with patient trust — and ultimately with the quality of patient care they are able to deliver.
So, choosing the right EHR software development company also plays a key role. A team with healthcare and compliance experience can help you avoid common mistakes, design secure architecture, and align the system with GDPR requirements from the beginning.
We’d be happy to talk

FAQ

An EMR system is GDPR compliant if it processes health data lawfully and protects it with appropriate safeguards. This includes data minimization, strong access control, data encryption, audit logs, and support for patient rights such as access and correction.
GDPR does not explicitly mandate encryption, but it strongly recommends it as a key security measure. In practice, encryption is expected to protect sensitive patient information both at rest and in transit, particularly when electronic health records contain biometric data or genetic data.
You maintain compliance through ongoing monitoring, regular security testing, updated risk assessments, and clear documentation. You also need processes for handling data subject requests, managing incidents, and reviewing access controls.
Appointing a data protection officer ensures ongoing accountability under applicable data protection laws, especially when processing personal health data at scale.
You apply privacy by design by integrating data security into the system from the start. This includes limiting data collection, restricting access based on roles, using secure defaults, and ensuring all data processing activities are clearly defined and controlled. Implementing robust technical and organizational measures also helps safeguard the vital interests of patients when their data is processed.

















 TechMagic Academy
TechMagic Academy