Phishing Attack Statistics 2026: Reasons to Lose Sleep Over
Last updated:9 March 2026
It's easy to think that only careless employees fall for phishing attacks. But what if that’s not the case? New phishing statistics reveal that senior executives are 23% more likely to fall victim to AI-driven, personalized attacks. Why?
Their busy schedules and the trust they place in authority figures make them prime targets.
Today, cybercriminals are going beyond exploiting technological gaps. They’re zeroing in on human behavior. Phishing incidents often exceed 5 million per month. Tactics like creating cognitive overload, leveraging trust in authority, and applying a sense of urgency make these attacks more effective. The data speaks for itself: these strategies are working.
In this article, we’ll not just list statistics on phishing attacks. We'll try to break them down to reveal what they really mean and explore the future of phishing campaigns. We’ll also look at their growing impact on businesses and what you need to do to stay ahead.
Key takeaways
- How common are phishing attacks? They now cause 36% of cybersecurity breaches.
- The number of phishing emails sent daily continues to grow. Threat actors use AI to make these attacks more advanced and harder to spot.
- AI is enabling faster, more personalized data-stealing malware, spear phishing emails, and phishing sites. By 2027, AI is predicted to be involved in 17% of cyberattacks.
- Finance, healthcare, and technology are prime targets. These industries hold valuable data and face higher risks from phishing attacks.
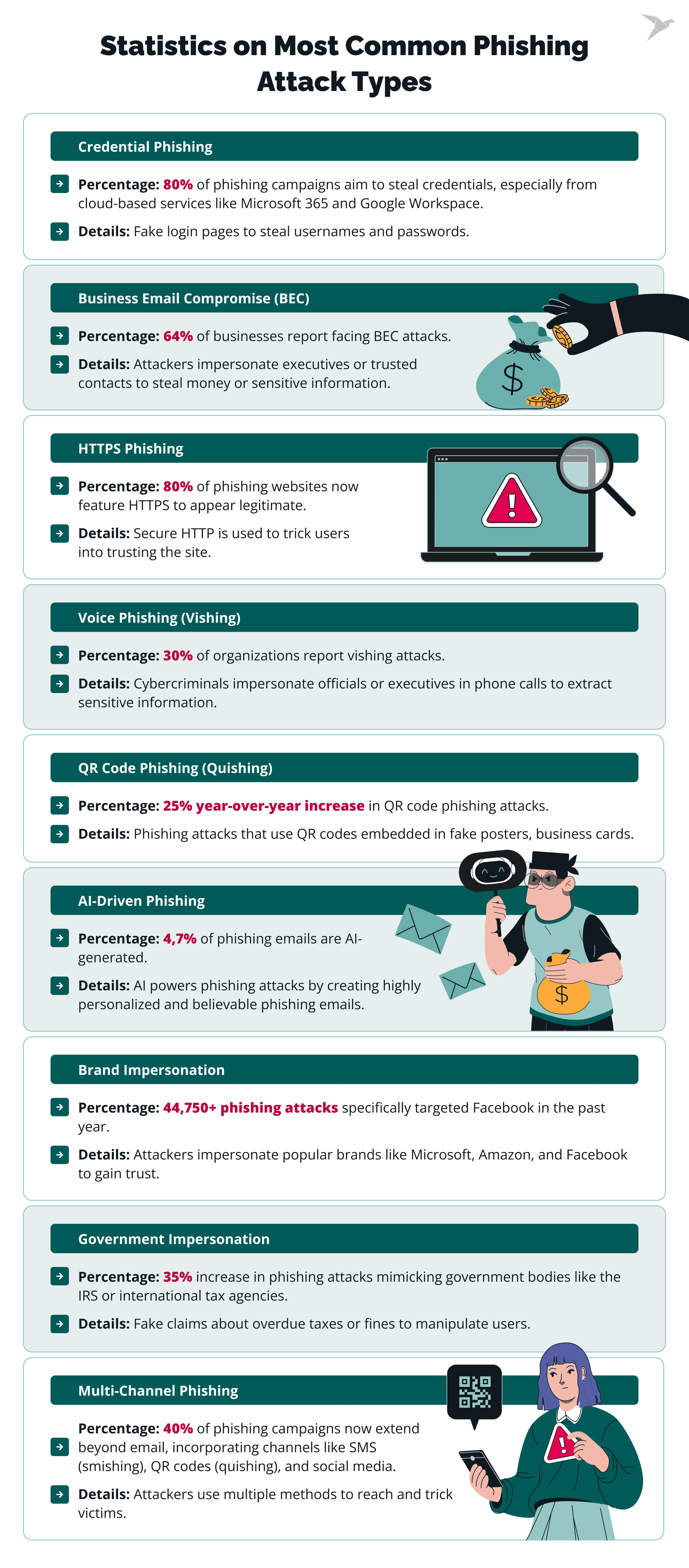
- Such phishing scams as BEC (business email compromise), credential phishing, and vishing (voice phishing) are the most common. New threats like quishing (QR code phishing) and AI-driven attacks are rising.
- Phishing breaches take an average of 254 days to identify and contain.
- Phishing scam statistics show that they caused $12.5 billion in losses, a 25% increase from the previous year. The average cost of a phishing breach is $4.9 million. Experts expect a lot of costly data breaches in the future.
- Phishing attacks, malicious messages, and online fraud now occur across email, SMS, social media, and phone calls, making them harder to detect.
Key Metrics of Phishing Attacks Statistics
The recent phishing attack statistics show that this type of digital fraud is indeed one of the most common in cybercrime and the dark web. Malicious emails often imitate legitimate sources in a very realistic way. Even skilled digital users will click on links or share personal information, leading to potential fraud or data security breaches.
Here are the numbers and facts that show the full picture:
- 30% of all cyber attacks begin with identity-based methods, such as phishing. It makes them the most common method for gaining initial access to corporate networks.
- 60% of small businesses view phishing, malware spam, and ransomware as major cyber security risks. They face significant risks, often not having the financial resources to recover.
- Around 80% of phishing campaigns aim to steal credentials, especially targeting cloud services like Microsoft 365 and Google Workspace. Microsoft is the most impersonated brand in phishing scams, appearing in 51.7% of attacks globally.
- 84% the number of phishing attacks involving infostealers rose in 2024.
- 180% increase in weekly volume of phishing attacks in 2025 compared to 2023.
Key Risks of Phishing Attacks
Phishing attacks evolve fast, exploit everyday behaviors, and can lead to devastating consequences for businesses. Phishing is responsible for 45% of all ransomware attacks. Here’s what you need to watch out for.
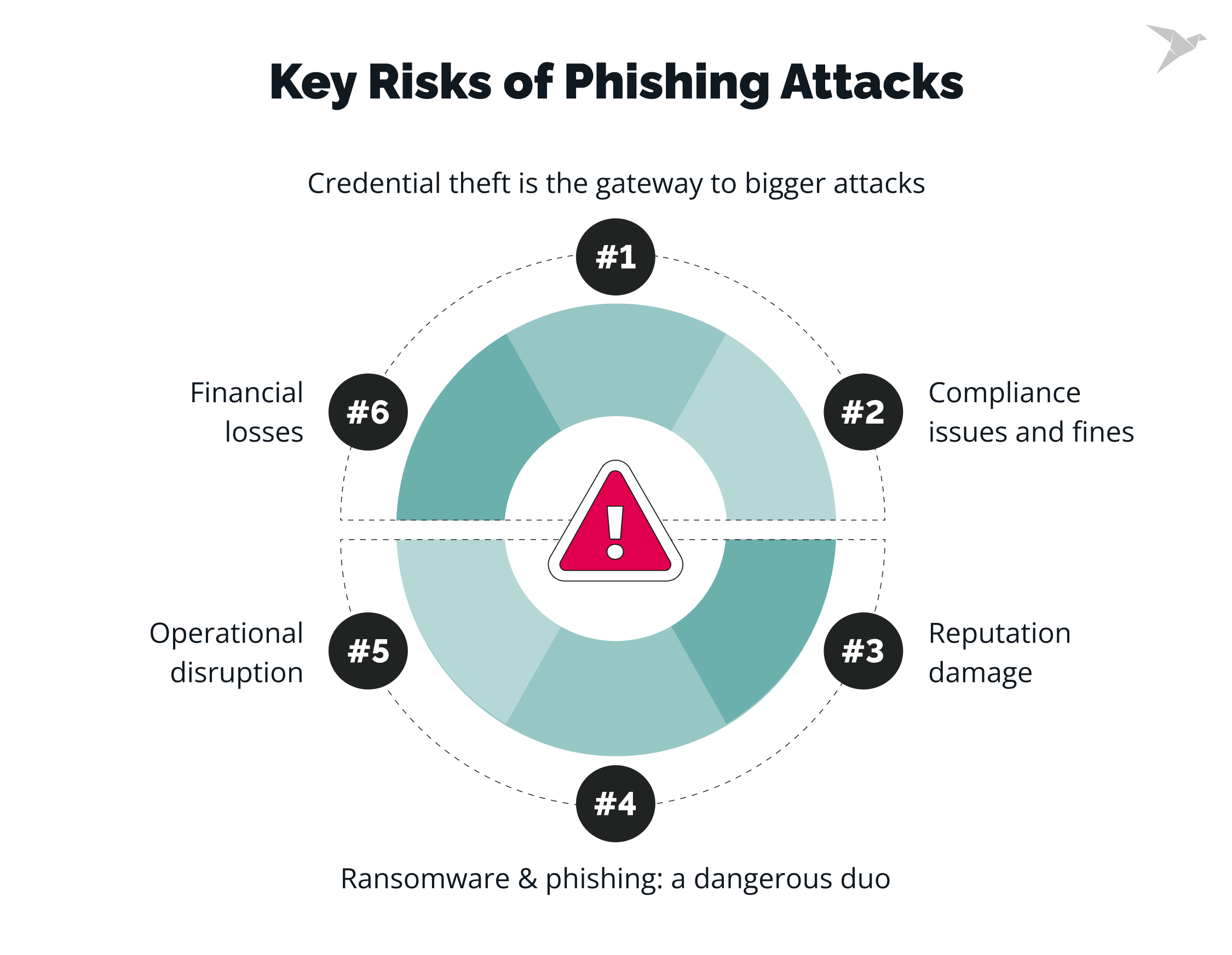
Credential theft is the gateway to bigger attacks
Phishing is the #1 method for accessing credentials, especially for cloud platforms like Microsoft 365 and Google Workspace. Attackers use fake login pages to make you think you're logging into the real thing, giving them easy access to sensitive data.
Ransomware & phishing: a dangerous duo
Phishing often leads to ransomware attacks. Once attackers steal your credentials, they can deploy ransomware, locking you out of your system. The cost of this combination can be sky-high, both in terms of recovery expenses and damage to your reputation.
Compliance issues
How many phishing emails do you get at work? Phishing is a leading method for gaining access to corporate networks. Once attackers get your employees' credentials, they can steal sensitive company data.
Businesses that suffer data breaches due to phishing often face legal action. In 100% of reported cyber crimes cases, it results in hefty fines and lawsuits that further damage their financial standing.
###Financial losses
Phishing attacks also lead to direct financial losses. Stolen credentials result in fraudulent transactions, and phishing-related ransomware can cost businesses millions to recover.
###Reputation damage
A successful phishing attack can severely harm your business’s reputation. Customers lose trust when their sensitive information is compromised, and rebuilding that trust can take years.
Operational disruption
The fallout from a phishing attack may result in operational downtime. It can take weeks or even months to fully recover, which means disrupted operations and decreased productivity during that period.
Our extensive expertise is at your disposal

Trends of Phishing Attacks
Let’s move on to trends formed by phishing attacks statistics.
Multi-channel attacks on the rise
41% of phishing incidents now involve multi-channel attacks, including SMS (smishing), QR codes (quishing), and voice calls (vishing).
Attackers are exploiting not only spam emails but also a variety of communication platforms like Slack, Teams, and social media, with 40% of phishing campaigns now extending beyond traditional email.
Moreover, 30.5% of phishing occurs through social media platforms, according to the Anti-Phishing Working Group (APWG). Social media phishing attempts continue to grow, using platforms’ trust and familiarity to deceive users.
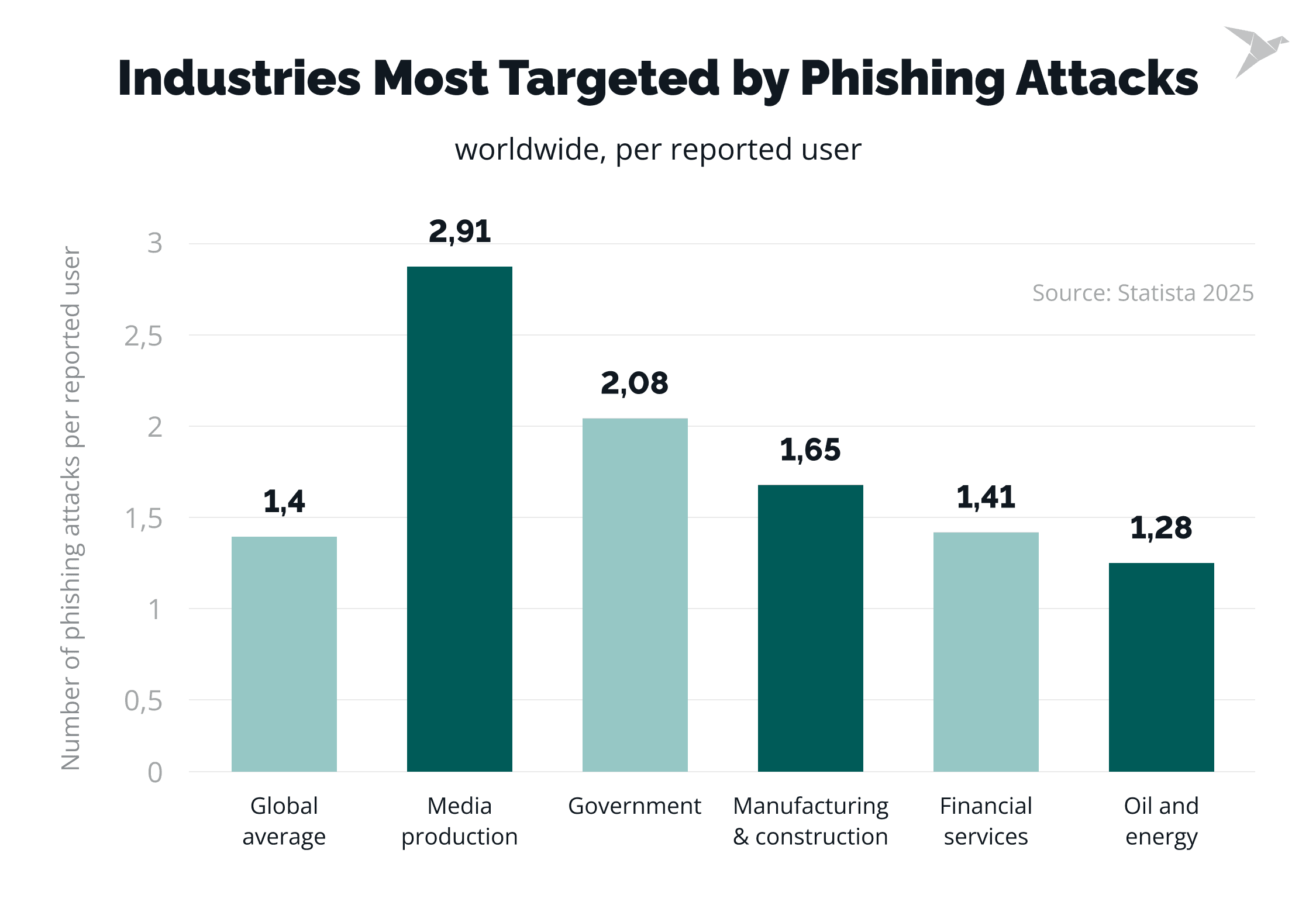
Impact on industries
Healthcare & Pharmaceuticals have the highest baseline Phish-prone Percentage (PPP), with 41.9% of employees likely to fall for malicious links and phishing. Insurance & Retail employees also exhibit high susceptibility, with PPPs of 39.2% and 36.5%, respectively.
Industries most targeted by AI-based attacks
Finance, healthcare, and government are the industries most targeted by AI-driven phishing and social engineering attacks.
Healthcare continues to face the highest breach-related costs of any industry. In 2025, the average healthcare data breach cost was about $7.42 million, marking the 14th straight year that the sector ranked first.
These incidents also take a long time to resolve. On average, healthcare organizations need about 279 days to detect and contain a breach, which adds to both the financial impact and the strain on day-to-day operations.
Another interesting fact: ransomware attacks led to an average of nearly 19 days of downtime for U.S. healthcare organizations. It is significantly affecting patient care and administrative functions.
Recent reports show that business email compromise (BEC) remains a major threat to financial organizations. According to the 2025 Verizon Data Breach Investigations Report, the median financial loss from a BEC incident is around $50,000, while 95% of loss-related cases range between $250 and $985,000.
Industry data also suggests that financial institutions are frequent targets. Research from APWG indicates that organizations in the financial sector face about a 70% chance of being targeted by a BEC attack in a given week.
Vulnerable user segments
New hires are highly vulnerable, with a 44% higher phishing click rate during their first 90 days of employment.
AI cyber attacks become more effective
We’ll discuss more numbers regarding using Artificial Intelligence and Machine Learning for phishing later. For now, pay attention that AI-powered multi-channel phishing campaigns have a 42% higher success rate than traditional email-only scams.
Real case
Cornell University's academic study imitated a mass phishing attack and sent over 71,000 emails (traditional, QR-code “quishing,” and LLM-enhanced). Results:
- Quishing was as effective as traditional phishing.
- LLM-generated phishing had click-to-landing success rates exceeding 30% in at least one company
Most phishing emails contain malicious attachments
94% of malware is delivered through email attachments. These phishing emails often lead to malware payloads or credential harvesting sites, putting businesses at risk of widespread compromise.
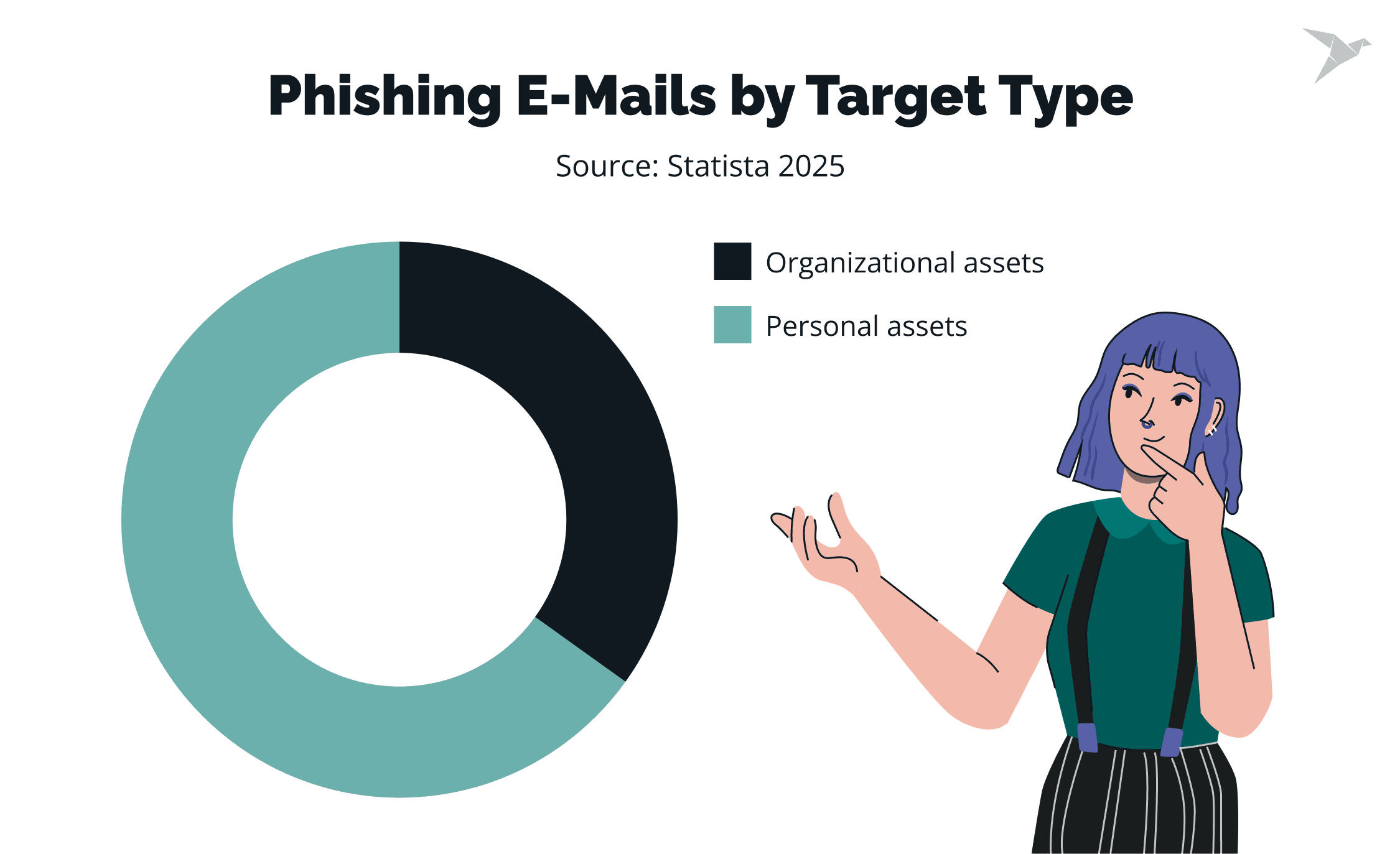
Personal Identifiable Information (PII) is a target
PII accounts for 46% of all stolen data in breaches, making it a primary target in phishing attacks. Phishing schemes are designed to harvest this valuable information for identity theft or fraud.
Impersonation campaigns use famous brands
Trusted brands like Microsoft and DocuSign are frequently impersonated in phishing campaigns. These familiar names and logos are exploited to make phishing attempts more convincing and difficult to detect.
In Q1 2025, Microsoft accounted for 36% of all brand phishing incidents worldwide, followed by Google at 12% and Apple at 8%
Sources: TechTarget, Gartner, McKinsey, Market and Markets, Statista
What is the Role of AI in Phishing Attacks
Phishing activity has risen dramatically in recent years. Some reports estimate that global phishing attempts increased by more than 4,000% after 2022. Generative AI is playing a role in this shift by making attacks easier to create. According to IBM, cybercriminals can now produce a convincing phishing email in around five minutes, whereas a human team previously needed about sixteen hours to craft a similar message.
For now, fully AI-generated phishing messages still represent a small portion of overall attacks. Gartner statistics of phishing attacks predict that generative AI will be involved in 17% of cyberattacks by 2027.
Even if the majority of phishing emails are sent by humans, artificial intelligence is still a powerful tool that attackers use very actively. Here are a few trends that are worrisome and definitely worth paying attention to.
AI-enhanced social engineering
AI is taking social engineering to the next level. Tools like deepfake videos and voice synthesis are allowing attackers to impersonate high-level executives and initiate fraudulent activities, such as wire transfers. While AI-generated phishing emails are still a small percentage, these sophisticated attacks are hard to detect and are becoming more common.
Scaling phishing with AI
AI is enabling attackers to scale their campaigns on phishing. With AI, they can send thousands of highly personalized phishing emails in seconds. This increased scale, combined with advanced tactics, makes these attacks more dangerous and harder to identify.
AI is now also helping attackers run multi-channel phishing cyber attacks, combining email, voice impersonation, deepfake videos, and live chat to maximize effectiveness.
Personalized attacks through AI
AI-powered attackers now use open-source intelligence from social media, corporate websites, and public records to personalize phishing messages. These tailored attacks are harder to spot and much more credible, making it easier for scammers to trick their targets.
This level of personalization increases the likelihood of successful phishing attempts, as attackers can mimic the victim's environment and make the scam feel more legitimate.
AI-Powered phishing kits
Although traditional phishing kits are still widely used, the growing availability of AI-powered kits is adding a new layer of complexity to the phishing landscape. These AI-driven tools automate the creation and distribution of convincing phishing emails, further pushing the boundaries of what attackers can achieve.
AI: A Growing Concern in Phishing Attacks
While AI-generated phishing emails still represent a small fraction of phishing incidents, the trend is growing rapidly. As AI continues to evolve, common phishing attacks will become more advanced, personalized, and harder to defend against. The shift to AI-driven phishing is already underway, and organizations must stay alert and prepared for the emerging risks it presents.
Sources: TechTarget, Gartner, McKinsey, Market and Markets, Statista
Top Phishing Statistics Insights for 2026
We’ve covered the basics, and now it’s time for a deep dive into the key insights into how phishing is impacting businesses globally.
How often do phishing attacks happen?
How common is phishing? 36% of all cybersecurity breaches involve phishing.
Over 3.4 billion phishing emails are sent every day, accounting for 1.2% of global email traffic.
94% of malware infections originate from it, and 80% of reported cybercrimes are attributed to phishing attacks.
What is the average phishing attack cost?
The average cost of a data breach involving phishing is around $4.9 million. This figure includes not only immediate recovery and response costs but also long-term repercussions, such as reputational damage and loss of customer trust.
How much money is lost to email scams every year?
Email-based fraud continues to grow. Recent FBI data shows that cybercrime losses reported in 2024 reached a record $16.6 billion, up 33% year over year, with email-driven scams still among the most common causes of financial harm.
The email channel itself also remains heavily abused. In 2025, security researchers found that nearly 45% of all global email traffic was spam, while the number of malicious email attachments exceeded 144 million, a 15% increase from the year before.
What percentage of phishing attacks are successful?
Phishing campaigns continue to evolve as attackers adopt new techniques. In 2025, global phishing activity increased by 58% year over year, while QR-code phishing attacks grew fivefold within just a few months. At their peak, security systems were blocking around 3 million QR-based phishing attempts per day, demonstrating how quickly these attacks can scale.
How many businesses are targeted by spear-phishing attacks?
Studies show that approximately 88% of organizations experience spear-phishing attacks annually. Attackers use a targeted approach where they impersonate trusted individuals or brands to trick employees into revealing sensitive data.
BEC phishing scams statistics
More sophisticated forms of phishing, such as spear phishing and business email compromise, have become more dominant. These attacks focus on specific people or companies, trying to steal important information or large amounts of money.
With the help of AI, these attacks are getting smarter, harder to notice, and more personalized to trick the victim.
- $4.67 million is the average cost of a BEC attack globally.
- $55.5 billion in exposed losses attributed to BEC scams globally.
- 13% increase in BEC attacks observed in February 2025 alone.
- 73% of BEC attacks originated from free webmail services.
- $487,000 is the average business interruption cost for SMEs hit by BEC.
To strengthen their defence against these attacks, businesses of all sizes use penetration testing services and social engineering testing services.

What percentage of cybersecurity incidents start with employees?
~ 80% of reported cybercrimes are attributed to phishing attacks that begin when an employee falls victim to a phishing attempt.
36% of breaches through phishing were the responsibility of employees.
Sources: KPMG, TechTarget, Market and Markets, IBM, Statista
Stay Ahead of Phishing and Cyber Threats with Tailored Security Solutions
Our cybersecurity team offers specialized services:
- full range of cybersecurity consulting services;
- different types of penetration testing and threat detection (including AI pen testing);
- phishing simulations (including spear phishing campaigns);
- social engineering services;
- security and phishing awareness training.
We focus on identifying all possible security vulnerabilities and strengthening your defenses with a tailored approach to your specific needs.
Phishing remains a major threat, with infostealers delivered via phishing emails increasing by 84%. Our simulations mimic real-world attacks to test employee response, uncover weaknesses, and offer secure data handling practices.
We provide ongoing security training to minimize human error and ensure your team is prepared to handle emerging threats. Our strategic, customized solutions keep your organization secure in a fast-changing threat landscape.

Final Thoughts: What Next?
The top phishing attack statistics show that phishing attacks are developing really fast. Over 50% of cybersecurity professionals highlighted the increasing sophistication of threats as a significant challenge. They also emphasize that outdated infrastructure remains a major barrier to tackling the arising cybersecurity risks.
Culture of cyber resilience and security training
By 2027, businesses must develop a culture of cyber resilience and security awareness training that integrates technology, people, and processes. This holistic approach will be essential for industries like energy, finance, and government, which face unique cybersecurity challenges in the age of advanced technologies.
Behavioral training and adaptive simulations are critical in improving cybersecurity resilience. Phishing success rates can be reduced by up to 86% with the right training programs. In particular, mobile-first phishing training is essential, as users are 25-40% more likely to fall for phishing attacks on mobile devices than on desktops. Phishing attacks cost large organizations $15 million annually, or more than $1,500 per employee.
So, businesses must take a proactive and holistic approach to cybersecurity. Focus on both technology and people, and your security posture will be better prepared to handle increasingly sophisticated phishing threats. Build resilience across departments, invest in adaptive defenses, and stay agile to get strong protection in 2026 and beyond.
FAQ

Phishing attacks involve tricking individuals into revealing sensitive information, such as passwords or financial details. These attacks often occur through fake emails or websites that appear legitimate.
Once a victim clicks a link or interacts with a fraudulent message, attackers can steal their data or gain unauthorized access to systems by impersonating trusted entities.
How often do phishing attacks happen? They now account for 36% of all cybersecurity breaches. The rise of AI and other technologies has made phishing attacks more sophisticated, with email-based phishing attacks delivering infostealers increasing by 84%. These advancements make it harder for traditional defenses to detect phishing, contributing to a higher success rate and greater frequency of incidents.
Finance, healthcare, and technology are the most affected sectors. Phishing scammers continue to target industries with valuable data or critical infrastructure.
These industries deal with sensitive information, making them prime targets for attacks like business email compromise and credential phishing. As digital dependence grows, these sectors face heightened risk and require stronger defenses to combat phishing threats.
In 2026 phishing stats, the most common types of phishing include business email compromise (BEC), where attackers impersonate executives to steal funds; credential phishing, which targets login details for cloud services; and voice phishing (vishing), where attackers impersonate trusted figures over the phone.
QR code phishing (quishing) is also on the rise, with attackers using fake codes to trick victims. AI-driven phishing is becoming more prevalent, enabling attackers to create personalized and harder-to-detect phishing emails. These evolving tactics make phishing attacks more challenging to defend against.

















 TechMagic Academy
TechMagic Academy





