Services
Discovery PhaseUX/UI Design
Web Development
Mobile DevelopmentTest AutomationData EngineeringCloud Services
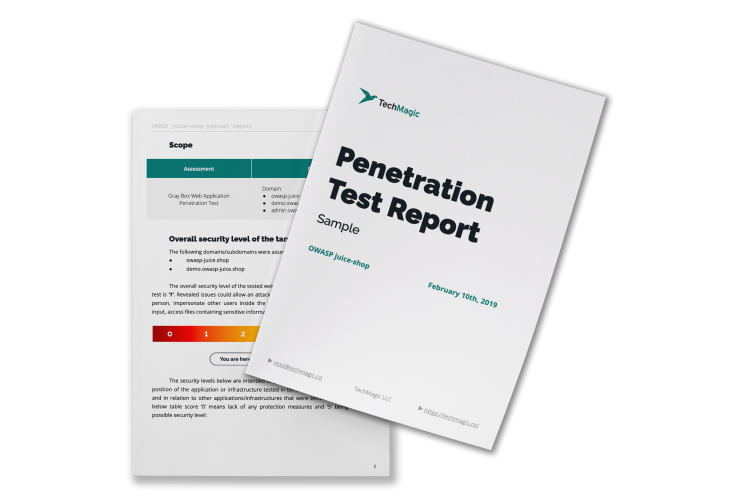
SalesforceSecurity
CTO-as-a-ServiceСlients
Case studies
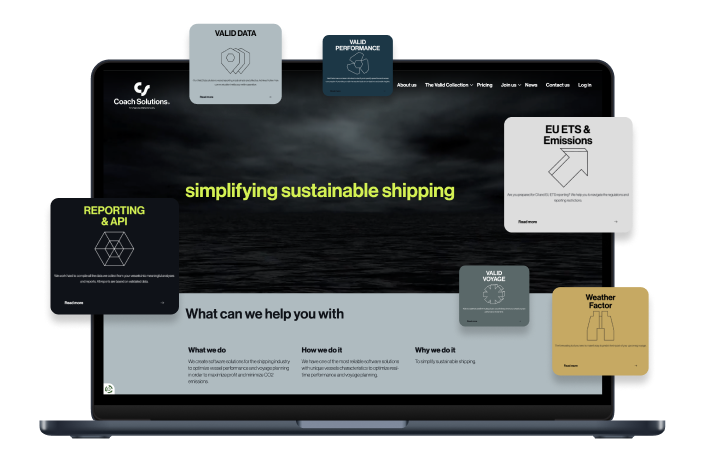
WendyAI-powered recruitment assistantBambooMicro-investment appCoin360Crypto exchange live data aggregatorCoach SolutionsWeb application penetration test
Elements CloudBusiness process visualization appAcorn-iIntelligent platform for ecommerceSqordSqord is the IoT fitness application for kids
Industries
Knowledge base